Getting Started
Introduction#
ComplyTime is a suite of open source tools designed to automate compliance workflows in cloud native environments. Our engineering-first approach brings compliance into your existing DevSecOps pipeline.
Architecture Overview#
ComplyTime spans two core domains Definition and Measurement integrated into your Software Development Lifecycle.
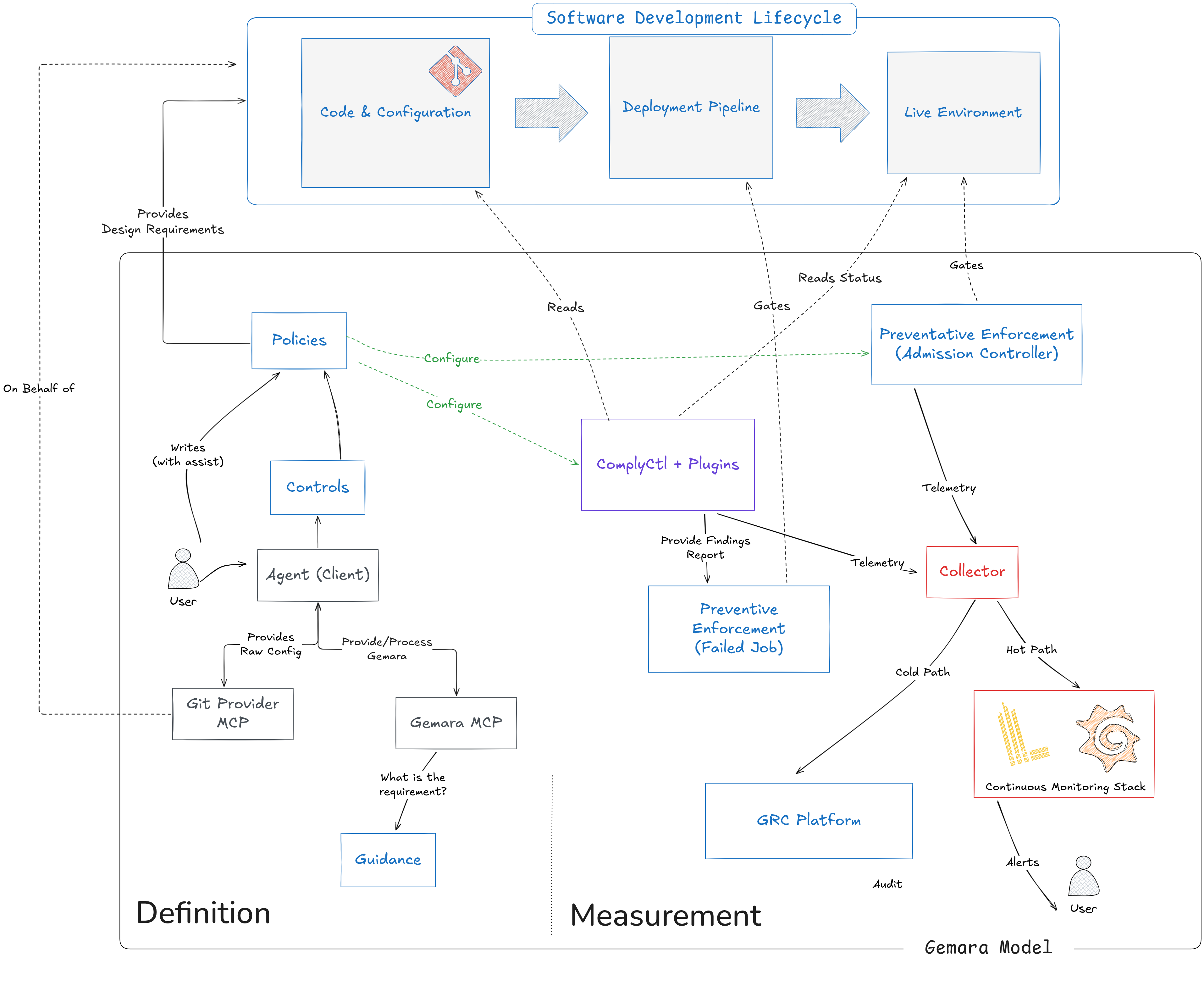
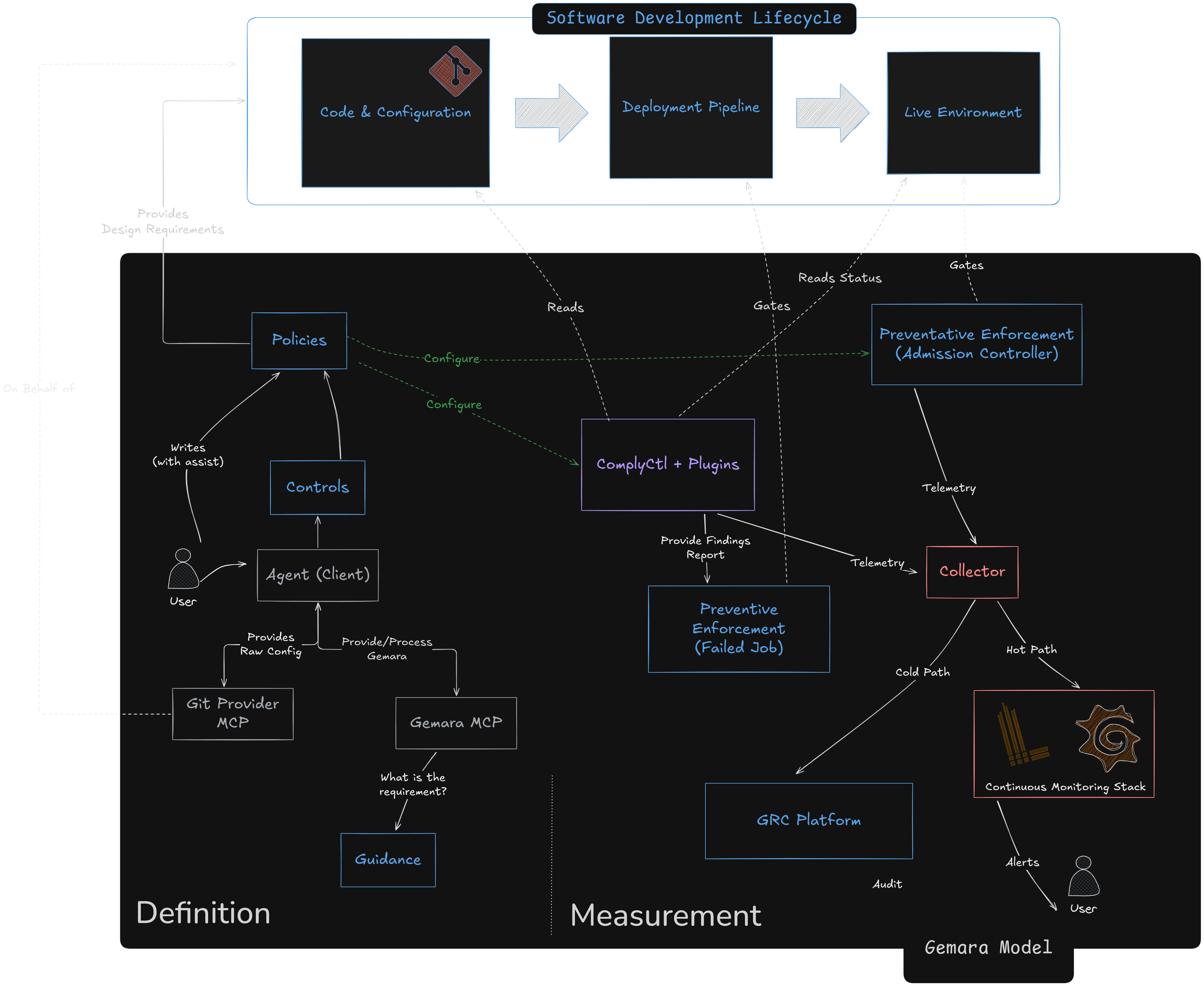
- Definition — Users author Policies and Controls (with AI assistance via the Gemara MCP Server), which are stored in Git and provide design requirements to the SDLC.
- Measurement —
complyctland its plugins read those policies, run assessments in the deployment pipeline, and feed findings to enforcement gates, a Collector, and downstream systems like GRC and Observability Platforms. - Preventative Enforcement — An Admission Controller gates the Live Environment in real time, while a failed-job mechanism blocks the pipeline when controls are not met.
Prerequisites#
Before you begin, ensure you have:
- Git for cloning repositories
To build from source, you will also need:
- Go 1.24+
- Make
Quick Start with complyctl#
The fastest way to get started is with complyctl, our command-line tool for compliance workflows.
Installation#
Binary (recommended)
Download the latest release from the complyctl releases page. Then verify the release signature using cosign:
cosign verify-blob \
--certificate complyctl_*_checksums.txt.pem \
--signature complyctl_*_checksums.txt.sig \
complyctl_*_checksums.txt \
--certificate-oidc-issuer=https://token.actions.githubusercontent.com \
--certificate-identity=https://github.com/complytime/complyctl/.github/workflows/release.yml@refs/heads/mainBuild from source
git clone https://github.com/complytime/complyctl.git
cd complyctl
make build
export PATH="$PWD/bin:$PATH"Verify Installation#
complyctl versionInstall a Scanning Provider#
Scanning providers are standalone executables placed in ~/.complytime/providers/. The filename determines the evaluator ID (e.g. complyctl-provider-openscap).
mkdir -p ~/.complytime/providers
cp bin/complyctl-provider-openscap ~/.complytime/providers/For the OpenSCAP provider, also install the required system packages:
openscap-scannerscap-security-guide
Your First Compliance Scan#
1. Initialize a workspace
complyctl initCreates a complytime.yaml workspace config. If one already exists, it validates and runs get automatically.
2. Fetch policies
complyctl getDownloads Gemara policies from the OCI registry into the local cache (~/.complytime/policies/). Uses Docker credential helpers — if docker login works, complyctl get works.
3. Verify the cache
complyctl list4. Generate assessment configuration
complyctl generate --policy-id <policy-id>5. Run the scan
# EvaluationLog (default)
complyctl scan --policy-id <policy-id>
# Markdown report
complyctl scan --policy-id <policy-id> --format pretty
# OSCAL assessment-results
complyctl scan --policy-id <policy-id> --format oscal
# SARIF
complyctl scan --policy-id <policy-id> --format sarifOutput is written to ./.complytime/scan/.
6. Check workspace health (optional)
complyctl doctor
complyctl providersNext Steps#
- Explore all ComplyTime projects